
Keeping clients' computers safe and profitable for over 30 years
Home Forms About Current Newsletter subscribe
Search All Articles
Browse by Category

How Miscreants make money by hacking your PC
Sometimes my clients (or potential clients) don't think they'll be attacked because, they don't have much on their computer, so what is it worth? This article shows how miscreants make money from attacking your computer even if you just use it for email. It is largely based on the Krebsonsecurity.com scrapped value of a hacked pc graphic.
Take control of your computer
They'll control your computer and bring it into their Botnet, which will:
- Extort money from sites threatening a Denial of service attack.
- Use your computer to do whatever illegal activities they want, traceable back to you not them.
- Attack a company with a Denial of Service attack
- Use your computer to click on links which are "pay per click" to defraud vendors.
- Use your computer to solve CAPTCHA puzzles.
- Use your computer to send out FBI fraud attacks: Your email will claim the recipient is downloading copyrighted materials or pornography and can avoid prosecution by paying a fine.
Ransomware
Ransomware is when they hold your computer or information hostage until you pay them money.- Fake antivirus attack (You've got 8,221 viruses. We'll clean them up for $69.95)
- Email Account Ransom (We won't give you your email back until you pay us).
- Data Ransom: They encrypt your hard drive, and won't decrypt it until paid
Email Attacks
They will use your computer to send out noxious and potentially damaging emails to your clients, friends and others on their target list.- Send out Spam to other people in your contact list as well as theirs.
- Harvest Email Addresses from your contact list and emails. Then they will try to infect them as well.
- Use your email account to access another account's password. For example, if your Amazon account or Paypal account can be told to reset your password, and send confirmation to you email account, the hacked email account will allow them to confirm the password change. This can give them full access to your other account. That account might allow them access to another account by resetting another password. Email accounts can be a wedge into much larger online identity theft.
- Attack others who would trust Email coming from you, either friends or your company.
- Send out phishing attacks from your computer. These are targeted attacks trying to convince your clients, or friends to go to some site and give them valuable information. For example, this is an example of a fraudulent phishing attack trying to be from a bank. Instead of going to the bank's website, your credentials are given to the miscreants so they can rob you or your clients or friends.
Sample Phishing scam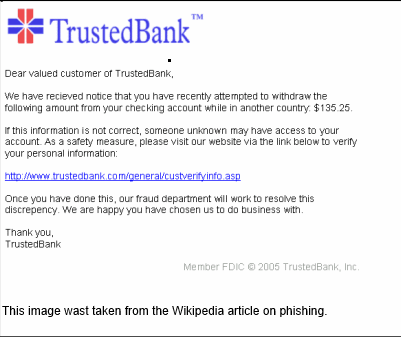
Get More Information
They will scavenge your computer hoping to find some other credential of some sort which they can then sell online.- Try and access your credit card, bank account, Stock trading or other financial information. These can be used or re-sold.
- Try and capture your Social Security number or other account passwords or login credentials. These can be used or re-sold.
Further Infections
They will not just give you a single infection. They will attempt to send you to other sites, capture links when you visit legitimate sites and send you elsewhere, and further infect your computer until it eventually gets so bogged down with malware that it no longer runs. Then they'll offer to fix it for you for a fee.Date: April 2013

This article is licensed under a Creative Commons Attribution-NoDerivs 3.0 Unported License.