Keeping clients' computers safe and profitable for over 30 years
Home Forms About Current Newsletter subscribe
Search All Articles
Browse by Category

Experts Versus Non-Experts
Three Google researchers used questionnaires and interviews with regular users and security experts to reveal differences on security practices and beliefs.
Highlights:
- Anti-Virus: Regular users tend to rely on their antivirus much more, and to overestimate its protective capacity. Experts don't emphasize antivirus software as much because it frequently can't recognize the newer attacks. They work to prevent the virus from ever getting on their computer. My antivirus program has not had a chance to protect me in well over a decade, because I don't make the mistakes necessary to enable viruses to access my computer. However, I still pay for an excellent antivirus program, just in case.
- Updates: Experts apply all software updates quickly, both for software and for their operating system. Regular users are much more lax about updating. I strongly urge my clients to use Ninite Updater to help them keep their software updated, and to apply their Windows patches soon after they are released.
- Passwords:
- Security experts emphasize using unique, long, random passwords. Regular users imagine they can reuse passwords passwords and often try to remember them.
- Security experts usually use a secure password safe like Keepass or Lastpass. Regular users are more likely to write them down and even distrust software vaults.
- Regular users think that changing passwords is a good idea and will make them more secure. Security experts only change their passwords if there is a good reason to. Regular password changing seldom improves security.
- Web Browsing:
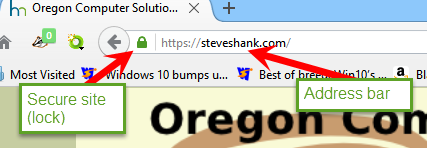
- Address Bar: Experts tend to check the address bar and look carefully at the URL to determine if the site is correct and if it is using HTTPS:. Regular users tend to not even know what the address bar is.
- Cookies: Regular users are more likely to imagine that deleting cookies will be useful. Experts are aware of how many other vectors for tracking exist so that cookies becomes small potatoes.
- Cautious: Security experts tend to be more suspicious of everything.
Two Factor Authentication
One place where I differ from other security experts is that I'm cautious of two factor authentication for general use, particularly when they do it by sending a code to your phone. It will protect you from a hacker trying to access your account with your password from another country or computer, but it is a hassle if you lose your phone, are out of cell coverage.
Furthermore, it requires that the company have a reset policy if you do lose your phone. What is that policy? Can a hacker break in using it? Here is a story of someone who was hacked because he had 2 factor authentication! Apparently, it isn't that hard to get your cell phone company to forward your cell phone number to another number!
It worries me that some people will use weaker passwords because they rely on the power of the 2 factor authentication.
It can also be a problem if you need a friend to access information for you. I stick with my 31 character random passwords which will work fine IF the website used proper encryption techniques and I do not lose control of my email account.
Further Reading
A detailed summaryhttp://googleonlinesecurity.blogspot.com/2015/07/new-research-comparing-how-security.html
The Full paper
https://www.usenix.org/system/files/conference/soups2015/soups15-paper-ion.pdf
Date: November 2015

This article is licensed under a Creative Commons Attribution-NoDerivs 3.0 Unported License.